Designing a Scalable OTA Strategy in Android Applications
#AndroidDevelopment #MobileArchitecture #ReleaseEngineering #ScalableApps
In Android development, OTA (Over-The-Air) updates are often misunderstood as simply “publishing a new build to the Play Store.”
At scale, OTA is not a release action.
It is an architectural control system.
In production-grade applications - especially commerce, fintech, or high-traffic platforms - how you design OTA directly impacts release velocity, revenue stability, and operational risk.
Let’s break it down.
1. Store-Based OTA: Binary Replacement Layer
When we:
Increment
versionCodeUpload AAB to Google Play Store
Use staged rollout
Monitor crash-free sessions
We are replacing the entire app binary.
This is mandatory for:
Native code changes
Dependency upgrades
SDK updates
Permission changes
Architecture refactors
Major UI changes (Compose/XML)
Limitations
Users may delay updates
Rollback is slow
Review delay risk
Emergency hotfix pressure
Binary OTA alone is not sufficient for high-scale apps.
2. In-App Updates: Version Enforcement Layer
Using the Play Core In-App Updates API, we can trigger:
Immediate Updates (blocking)
Flexible Updates (background download)
A clean architecture pattern:
Backend:
minSupportedVersion = 120
recommendedVersion = 125
App Launch:
if currentVersion < minSupportedVersion:
triggerImmediateUpdate()
else if currentVersion < recommendedVersion:
showFlexibleUpdate()
This avoids hardcoded force-update logic.
It also gives product and backend teams controlled rollout authority.
3. Runtime OTA: Remote Config & Feature Flags
The real maturity layer.
Instead of shipping logic changes through Play Store:
We separate:
Binary Layer → Structural changes
Config Layer → Business rules
Experiment Layer → Feature flags
Using runtime configuration, we can control:
Cashback calculation toggles
Discount stacking logic
Payment provider routing
Checkout flow variants
UI experiments
Kill switches for risky modules
This reduces emergency releases significantly.
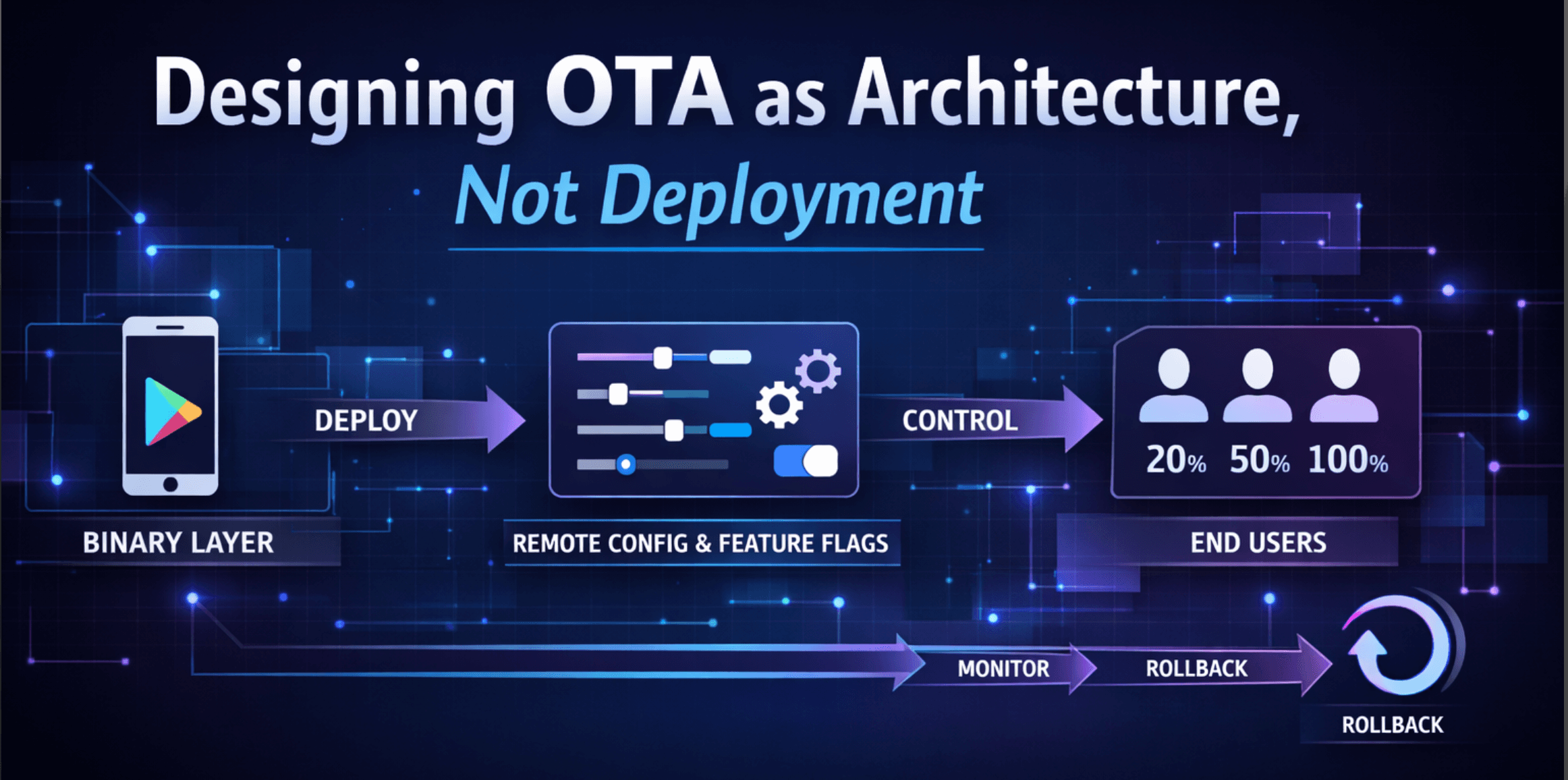
4. Production-Grade OTA Architecture
A scalable startup sequence:
App Start
↓
Load Cached Config
↓
Fetch Remote Config (Async)
↓
Validate App Version
↓
Apply Feature Flags
↓
Render UI
With:
Safe defaults
Config expiry control
Kill switches
Version-based flag targeting
Rollback capability
This transforms OTA into:
A risk management layer
A velocity enabler
A runtime control system
5. Engineering Insight
In mature Android systems:
Deployment ≠ Release
Release ≠ Exposure
You can:
Deploy code → Keep feature OFF
Enable feature → 5% users
Scale to 100% → Monitor metrics
Instantly disable → If anomaly detected
This is how large-scale mobile systems operate safely.
Final Thought
If your OTA strategy is only “push a new build”, you are operating at a surface level.
If your OTA strategy includes runtime control, version gating, and safe rollout architecture, you are building production-grade mobile systems.
If you’re designing large-scale Android systems, OTA should be treated as architecture, not deployment.